Conflicting issues with the LoadBalancer and the way in which Kubernetes functions could trigger connection timed out error during http-01 challenge propagation,
Here are IbmiMedia, We have helped customers fix LoadBalancer and Kubernetes related errors as part of our Server Support Services.
In this context, we shall look into this error and how to fix it.
More about connection timed out error during http-01 challenge propagation
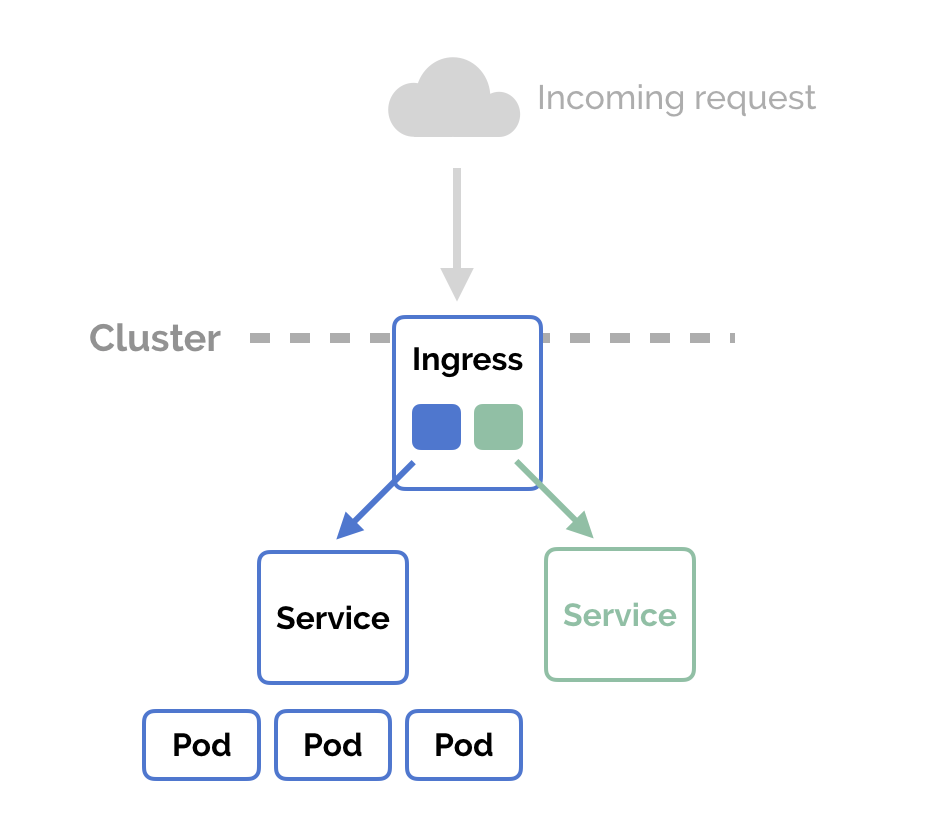
A Kubernetes Ingress helps to expose Services inside of your cluster to the outside of the cluster via compacting the routing rules to a single resource. Its aim is to boost performance and provide more options to work with such rules.
Nginx, HAProxy, Contour and Traefik are common Ingress Controllers.
Just recently, we experienced the following errors with generating Certificates when trying to configure Nginx Ingress with Cert-Manager on DigitalOcean Kubernetes to use HTTPS in the cluster;
Waiting for http-01 challenge propagation: failed to perform self check GET request 'http://cert-test.ibmimedia.com/.well-known/acme-challenge/jC9hDBr5qI018y1gqacU2BbytGBb30YfQHcCyUx1kEY': Get http://cert-test.ibmimedia.com/.well-known/acme-challenge/jC9hDBr5qI018y1gqacU2BbytGBb30YfQHcCyUx1kEY: dial tcp 123.432.008.80:80: connect: connection timed out
As already stated earlier, Conflicting issues with the LoadBalancer and how Kubernetes functions functions could trigger a connection timed out error.
DigitalOcean LoadBalancer feature may have Kubernetes not routing network via the public interface of the LoadBalancer.
Therefore, in this process SSL or PROXY protocol header may not be added when exposing it outside the cluster by Kubernetes.
Thus, the cert-manager will not be able to reach the public domain name as it functions only the outside of the cluster and not within. A way of finding a resolution would be to add some directives whereby the PROXY protocol will be forced to bypass the validator to obtain the Certificates.
What to do to fix connection timed out error during http-01 challenge propagation
To resolve this error, follow the steps below;
i. To begin, you have to create a dedicated DNS entry point to the public IP of your Load balancer. Then you can check for EXTERNAL-IP via `kubectl get svc -n ingress-nginx), eg. ibmimedia.website.com
ii. Add an annotation in the manifest used to create the loadbalancer referencing to the DNS entry created. It will look like this;
annotations: service.beta.kubernetes.io/do-loadbalancer-hostname: "ibmimedia.website.com"
Additionally, you can also set in your LoadBalancer externalTrafficPolicy to Cluster.
Need support in fixing Kubernetes errors? We are here to help.
Conclusion
Best fix to "Connection timed out" error during http-01 challenge propagation.
Best fix to "Connection timed out" error during http-01 challenge propagation.