The values assigned in a PowerShell Execution Policy can trigger the "PowerShell is not a digitally signed" error.
This error occurs sometimes when users run PowerShell scripts.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our customers to fix Windows related issues.
Now, let us look into how to solve this error.
What causes PowerShell is not digitally signed error?
The security error "PowerShell is not digitally signed" occurs when dealing with PowerShell Script which is not signed by a Trusted Publisher.
Additionally, when an AllSigned or RemoteSigned PoerShell Execution Policy is used, the security error can occur.
How to fix "PowerShell is not digitally signed" error?
To fix this error, different methods can be applied as will be shown below.
i. Inspect and Modify the Execution Policy.
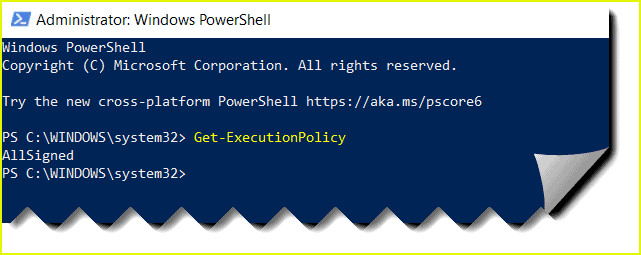
To get the Execution Policy, simply run the "Get-ExecutionPolicy" cmdlet. The policy for each scope is described by the parameter in the Get-ExecutionPolicy cmdlet as shown below;
PS C:\> Get-ExecutionPolicy -listAdditionally, you can set the execution policy to Unrestricted and modify the Execution Policy via the SetExecutionPolicy cmdlet by running the command below;
PS C:> Set-ExecutionPolicy unrestrictedThen when prompted to continue, Press "Y" to change the Policy.
ii. Bypassing the current PowerShell session
Another method of fixing this issue is by modifying the execution policy temporarily by running the Set-ExecutionPolicy cmdlet with Bypass setting as shown below;
Set-ExecutionPolicy -Scope Process -ExecutionPolicy ByPassThis will help to set the execution policy to bypass the current PowerShell session. Since this is temporal, as soon as the PowerShell session is closed, the settings will be lost.
iii. Unblocking the downloaded file
You can sign all the scripts and its configuration files downloaded from an external source (Internet) or from a trusted publisher's email.
If the contents of the script are safe and trusted, then you can implement an unblock by running the Unblock-File cmdlet as shown below;
PS C:> Unblock-File -Path C:Downloadsscript1.ps1Important values for ExecutionPolicy parameter
We will look briefly at the some acceptable values for -ExecutionPolicy parameter;
1. Restricted
This restricts the script from running and also prevent the configuration files from loading. It is regarded as the default execution policy.
2. AllSigned
This requires that a trusted publisher signs all script and configuration files including scripts written on the local computer.
3. RemoteSigned
All scripts and configuration files downloaded from the internet is signed by a trusted publisher.
4. Unrestricted
This allows all scripts and configuration files to load. However, you will be prompted for permission when trying to run an unsigned script downloaded from the internet.
5. Bypass
This allows Scripts and Configuration files to run without any interruptions or warnings.
6. Undefined
This takes off the currently assigned execution policy from the current scope. However, an execution policy configured in a Group Scope will not be altered.
LocalMachine is the default scope for Set-ExecutionPolicy command. By adding the "-Scope" parameter, you can specify the scope for policy. Some scopes you can work with includes the following;
Process: Only the current PowerShell process is affected by the execution policy.
CurrentUser: Only the current user is affected by the execution policy.
LocalMachine: Here, all users of the computer is affected by the execution policy.
Need support in fixing Powershell is not digitally signed error? We are available to help you today.
Conclusion
This article will put you through the steps to fix "PowerShell is not digitally signed" security error which can be triggered when PowerShell Execution Policy is set to AllSigned or RemoteSigned.
This article will put you through the steps to fix "PowerShell is not digitally signed" security error which can be triggered when PowerShell Execution Policy is set to AllSigned or RemoteSigned.