Systems Administrators make use of Local Group Policy Editor in Windows to prevent anonymous login and ban IP of attacker through IPban.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to keep their servers safe from attacks.
In this context, we shall look into the steps to combat anonymous login in Windows.
Why is it important to prevent anonymous login and ban IP of attacker in Windows?
In most of the Network, webmasters might want users to anonymously log on and log off for certain machines. This is certainly true of all public Web and FTP servers. But for the rest of the network, allowing anonymous login is a security risk that need to be lock down.
For instance the NT Authority/Anonymous event ID 528 (Logon) Type 3 on your file servers and workstations is suspicious. These events indicate that an anonymous user has successfully viewed or connected to a network share.
We can fix this type of vulnerabilities by disabling anonymous login by using Local Group Policy Editor. Let us now look at the steps to perform it on Windows Server 2008 R2.
How to restrict anonymous login and ban IP of attacker in Windows?
i. On Windows Server 2008 R2 / Windows Server 2012, to open the Local Group Policy Editor, click Start button, type gpedit.msc in the Start Search box, and then press ENTER.
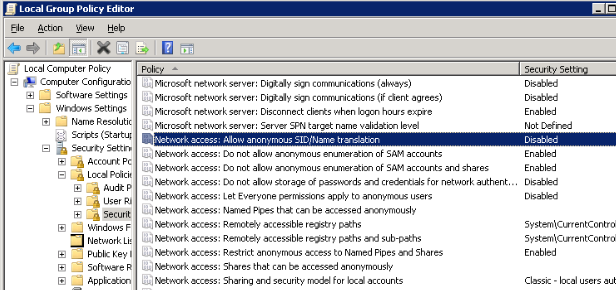
ii. Under Computer Configuration\Windows Settings\SecuritySettings\Local Policies\SecurityOptions, there are 6 policies under network access to control what information can be accessed anonymously.
iii. Disable the policies to “Allow anonymous SID/Name translation” and “Let Everyone permissions apply to anonymous users”.
iv. Enable the policies for “Do not allow anonymous enumeration of SAM accounts” and “Do not allow anonymous enumeration of SAM accounts and shares”.
v. Clear empty the policies for “Named Pipes that can be accessed anonymously” and “Shares that can be accessed anonymously”.
In addition to disabling anonymous login, installing applications for endpoint protection will help to prevent attempts to attack on the server.
How to protect servers that use Remote Desktop?
If we use Remote Desktop to connect to the server, we can do a security layer by the steps below:
1. Change the default service port of Remote Desktop and the server.
2. Use IPBan which is a free tool to track any IP that invokes services on the server. When number of fail events reaches to a predefined threshold, it will block the IP in the Windows Advanced Firewall by using a Blocking rule there.
How to set up IPBan?
IP ban can be downloaded from the link here . .NET Framework 4 is required for IPBan. The main configurations to set it up and run include:
i. Config Remote Desktop Session Host Configuration to log IP address in event log.
To run it: click Start button, key Remote Desktop Session Host Configuration in the Start Search box, and then press ENTER. Double click the connection RDP-Tcp to change encryption settings to native RDP encryption. Set the Security Layer to RDP Security Layer and click on OK. After finishing, please reboot your server.
ii. Copy IPBan binary to a folder, e.g. D:\IPBan. Then open and modify IPBan.exe.config file. Modify the Group rules, rule for attempts before banning, ban time rule and log file rotation rule.
iii. Create IPBan service and start it;
#sc create IPBan type= own start= auto binPath= D:\IPBan\ipban.exe DisplayName= IPBan
#net start IPBan[Need urgent assistance in fixing Windows errors? – We're available 24*7. ]
Conclusion
This article will guide you on the steps to Restrict anonymous login and ban #IP address of attacker by using Local Group Policy Editor in #Windows which allows us to prevent anonymous login and #IPBan helps to ban IP of #attacker.
This article will guide you on the steps to Restrict anonymous login and ban #IP address of attacker by using Local Group Policy Editor in #Windows which allows us to prevent anonymous login and #IPBan helps to ban IP of #attacker.