Are you trying to disable NetBIOS and LLMNR Protocols?
We can help you.
The broadcast protocols NetBIOS over TCP/IP and LLMNR are used in most modern networks only for compatibility with legacy Windows versions.
However, both protocols are susceptible to spoofing and MITM attacks. For improving network security, we can disable these protocols on the domain network.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to use Windows servers to disable both NetBIOS and LLMNR.
In this context, we shall look into to method to disable these protocols in Windows.
How to Disable NetBIOS and LLMNR Protocols ?
NetBIOS and LLMNR protocols allow computers on the local network to find each other if the DNS server is unavailable.
LLMNR (UDP/5355, Link-Local Multicast Name Resolution) is used in all Windows versions starting from Vista and allows IPv6 and IPv4 clients to resolve the names of neighboring computers without using DNS server due to broadcast requests in the local L2 network segment.
NetBIOS over TCP/IP or NBT-NS (UDP/137,138;TCP/139) is a broadcast protocol being a predecessor of LLMNR and used in the local network to publish and search for resources.
They are needed in a workgroup environment.
However, in a domain network, we can disable both of these protocols.
1. Disabling LLMNR on Windows Using GPO
We can disable the LLMNR protocol on a Windows computer locally via the registry using the following PowerShell commands:
New-Item "HKLM:\SOFTWARE\Policies\Microsoft\Windows NT" -Name DNSClient -Force
New-ItemProperty "HKLM:\SOFTWARE\Policies\Microsoft\Windows NT\DNSClient" -Name EnableMultiCast -Value 0 -PropertyType DWORD -ForceFollowing are the steps to disable using Group Policy:
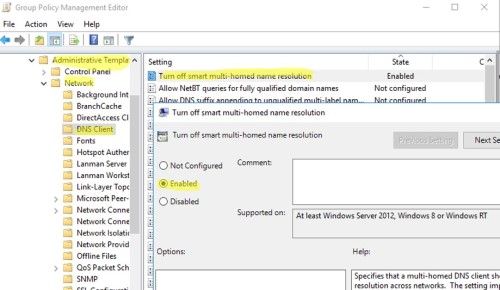
i. First, open the gpmc.msc, create a new GPO or edit an existing one that is applied to all workstations and servers.
ii. Then go to Computer Configuration and take Administrative Templates.
iii. From there, go to Network and take DNS Client.
iv. After that, we need to enable Turn off smart multi-homed name resolution policy by changing its value to Enabled.
v. Wait while the GPO settings on clients are updated or manually update them using the following command:
$ gpupdate /force2. Disabling NetBIOS over TCP/IP via Group Policy
There is no separate GPO option that allows disabling NetBIOS over TCP/IP for all network adapters in Group Policy Editor.
We can use the following PowerShell logon script to completely disable NetBIOS for all network adapters:
$regkey = "HKLM:SYSTEM\CurrentControlSet\services\NetBT\Parameters\Interfaces"
Get-ChildItem $regkey |foreach { Set-ItemProperty -Path "$regkey\$($_.pschildname)" -Name NetbiosOptions -Value 2 -Verbose}We can save this code to disableNetbios.ps1 file, copy it to the GPO directory.
To run on clients via Computer Configuration we can do the following steps:
i. Go to Policies in the computer configuration
ii. And take Windows Settings
iii. From there go to Scripts
iv. After that take Startup and go to PowerShell Scripts.
v. If our current PowerShell execution policy is blocking this script from running on Windows computers, we must sign the PS1 script or run it in bypass mode.
vi. For this change to take effect, we have to enable/disable network adapters or restart the computer.
vii. Then open a command prompt and run the following command in order to check that NetBIOS is disabled for the network adapters :
wmic nicconfig get caption,index,TcpipNetbiosOptions[Need assistance in fixing Windows errors? We can help you. ]
Conclusion
This article covers how to disable NetBIOS and LLMNR Protocols for our customers. The broadcast protocols NetBIOS over TCP/IP and LLMNR are used in most modern networks only for compatibility with legacy Windows versions. Both protocols are susceptible to spoofing and MITM attacks.
In the Metasploit there are ready-made modules that allow you to easily exploit vulnerabilities in the broadcasting NetBIOS and LLMNR protocols to intercept user credentials in the local network (including NTLMv2 hashes).
To improve your network security, you need to disable these protocols on the domain network.
In the domain environment, LLMNR broadcasts can be disabled on computers and servers using Group Policy.
To do it:
1. Open the gpmc.msc, create a new GPO or edit an existing one that is applied to all workstations and servers;
2. Go to Computer Configuration -> Administrative Templates -> Network -> DNS Client;
3. Enable Turn off smart multi-homed name resolution policy by changing its value to Enabled;
4. Wait while the GPO settings on clients are updated, or manually update them using the command: gpupdate /force.
To manually disable NetBIOS on Windows as follows:
1. Open network connection properties
2. Select TCP/IPv4 and open its properties
3. Click Advanced, then go to WINS tab and select Disable NetBIOS over TCP
4. Save the changes.
This article covers how to disable NetBIOS and LLMNR Protocols for our customers. The broadcast protocols NetBIOS over TCP/IP and LLMNR are used in most modern networks only for compatibility with legacy Windows versions. Both protocols are susceptible to spoofing and MITM attacks.
In the Metasploit there are ready-made modules that allow you to easily exploit vulnerabilities in the broadcasting NetBIOS and LLMNR protocols to intercept user credentials in the local network (including NTLMv2 hashes).
To improve your network security, you need to disable these protocols on the domain network.
In the domain environment, LLMNR broadcasts can be disabled on computers and servers using Group Policy.
To do it:
1. Open the gpmc.msc, create a new GPO or edit an existing one that is applied to all workstations and servers;
2. Go to Computer Configuration -> Administrative Templates -> Network -> DNS Client;
3. Enable Turn off smart multi-homed name resolution policy by changing its value to Enabled;
4. Wait while the GPO settings on clients are updated, or manually update them using the command: gpupdate /force.
To manually disable NetBIOS on Windows as follows:
1. Open network connection properties
2. Select TCP/IPv4 and open its properties
3. Click Advanced, then go to WINS tab and select Disable NetBIOS over TCP
4. Save the changes.