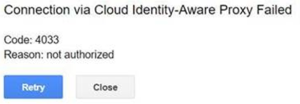
Basically, Google Error Code 4033 happens when you don't have permission to access the instance, the instance doesn't exist or the instance is stopped.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to perform related Google Cloud queries.
In this context, we shall look into how to fix this Google Cloud error.
How to resolve Google Cloud Error Code 4033 ?
To begin, make sure that you apply the AP-secured Tunnel User IAM role on the resource we connect. We can check it on the Identity-Aware Proxy page.
The most important thing to do is to Check if your firewall rules allow SSH connection, you should look for default-allow-ssh and ensure that the firewall settings are correct.
Apply the follow tips to resolve this issue.
1. Manage access to IAP-secured resources
With IAP we can configure IAP policies for individual resources in a Google Cloud project. Within the project, different apps can have different access policies.
We can manage project level and higher access via the IAM admin page.
You can turn IAP on and off.
To turn IAP on and off, we need certain permissions:
1. App Engine require appengine.applications.update
2. Compute Engine or Google Kubernetes Engine require;
compute.backendServices.update
Roles such as Project Editor, App Engine Admin, and Compute Network Admin grant us these permissions.
Though they allow turning IAP on and off, they don’t have the permissions to modify access policies.
In addition, we require the clientauthconfig.clients.create and clientauthconfig.clients.getWithSecret permissions to turn IAP on with the Cloud Console.
2. Manage access in the Cloud Console
In order to add or remove access, we suggest following the below process.
To Add access:
i. Initially, we go to the Identity-Aware Proxy page.
ii. We select the resource to secure with IAP. The below selections secure a set group of resources:
a) All Web Services.
b) Backend Services.
iii. Then on the Info panel, we add the email addresses to grant an Identity and Access Management role.
iv. We apply access policy roles to the member from the following roles in the Select a role dropdown:
a) Owner: Grants the same access as IAP Policy Admin.
b) IAP Policy Admin: Grants administrator rights over IAP policies.
c) IAP-Secured Web App User: Grants access to the app and other HTTPS resources that use IAP.
d) Security Reviewer: Grants permission to view and audit IAP policies.
v. Once we finish adding email addresses and setting roles, we click Add.
To Remove access:
i. Firstly, we go to the Identity-Aware Proxy page.
ii. Then we select the resource secured with IAP.
iii. On the Info panel, we select the section that corresponds to the role we want to remove from a member.
iv. In the expanded section, next to each user or group name to remove the role, we click Remove.
v. Then in the Remove member dialog that appears, we click Remove.
3. Manage access with the API
Here, let us see a standard set of methods IAM provides to create and manage access control policies.
i. Resources and Permissions:
With the IAP API, we can apply IAM permissions to individual resources in an IAP-secured project.
Generally, if we grant the IAM permissions at a certain level, it applies to all levels underneath it.
For example, project-level permissions apply to all Google Cloud resources in the project. Access for project-level and above is managed in the IAM admin page but will display on the IAP admin page.
To access an IAP-secured app and use methods that update IAM policies, we need permission.
The iap.webServiceVersions.accessViaIAP permission grants access to the app.
On the other hand, we need iap.tunnelInstances.accessViaIAP permission if we use the IAP to control access to administrative services like SSH and RDP.
Each IAP resource has its own getIamPolicy and setIamPolicy permissions. They grant the ability to manage access policies for that resource and its children.
ii. Public access:
To grant everyone access to a resource, we add one of the following members to its access list:
- allAuthenticatedUsers: Anyone who authenticates with a Google account or a service account.
- allUsers: Anyone who is on the internet.
If we grant public access, IAP won’t generate Cloud Audit Logs logs for the request.
In addition, bindings that grant public access can’t have a condition associated with them.
For example, a policy that allows anyone accesses to a resource if the request path starts with /public/ is invalid.
a. Roles
IAP-Secured Web App User (roles/iap.httpsResourceAccessor) includes permission, iap.webServiceVersions.accessViaIAP.
b. Grants access to App Engine and Compute Engine resources.
IAP-Secured Tunnel User (roles/iap.tunnelResourceAccessor) includes permission, iap.tunnelInstances.accessViaIAP.
c. Grants access to tunnel resources that use IAP.
IAP Policy Admin (roles/iap.admin) includes permissions, iap.web.getIamPolicy, iap.web.setIamPolicy, iap.webTypes.getIamPolicy, iap.webTypes.setIamPolicy, iap.webServices.getIamPolicy, iap.webServices.setIamPolicy, iap.webServiceVersions.getIamPolicy, iap.webServiceVersions.setIamPolicy.
Grants IAP administrative rights to manage IAP access policies of resources.
[Finding it hard to fix Google Cloud issues? We are here for you. ]
Conclusion
This article covers methods to resolve Google Cloud Error Code 4033. Virtual Private Cloud (VPC) firewall rules apply to a given project and network. If you want to apply firewall rules to multiple VPC networks in an organization.
VPC firewall rules let you allow or deny connections to or from your virtual machine (VM) instances based on a configuration that you specify. Enabled VPC firewall rules are always enforced, protecting your instances regardless of their configuration and operating system, even if they have not started up.
This article covers methods to resolve Google Cloud Error Code 4033. Virtual Private Cloud (VPC) firewall rules apply to a given project and network. If you want to apply firewall rules to multiple VPC networks in an organization.
VPC firewall rules let you allow or deny connections to or from your virtual machine (VM) instances based on a configuration that you specify. Enabled VPC firewall rules are always enforced, protecting your instances regardless of their configuration and operating system, even if they have not started up.