Sometimes in the process of installing the latest updates on Windows 10 desktop, Windows users experiences "RDP authentication error has occurred" error.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to fix Windows related errors.
In this context, we shall look into the main causes of this error and how to fix it.
What triggers "RDP authentication error has occurred" problem?
As earlier stated, this RDP error occurs after installing the latest security updates on Windows 10 desktop. However, these updates fix a serious vulnerability in the CredSSP protocol used for authentication on RDP servers.
But these updates are not installed on the RDP/RDS server-side, and the NLA (Network Level Authentication) is enabled for remote desktop access.
Therefore, the computer blocks the remote desktop connection to a server that uses the vulnerable version of CredSSP.
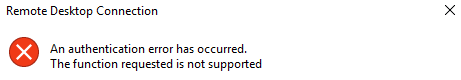
For example, the error appears as below;
rdp authentication error has occurredHow to fix "RDP authentication error has occurred" issue?
To solve this issue, you can apply the following methods;
Method 1
The best way to resolve this problem is to install the latest cumulative Windows security updates on a remote computer or RDS server.
Method 2
We try to disable the NLA (Network Level Authentication) on the RDP server side. Here are the steps for it.
If NLA is enabled on the RDP server then it means that CredSSP is used for RDP user's pre-authentication. So, we disable the Network Level Authentication in the System Properties on the Remote tab by unchecking the options "Allow connection only from computers running Remote Desktop with Network Level Authentication (recommended)" (Windows 10 /8.1 or Windows Server 2012R2/2016).
In Windows 7 (Windows Server 2008 R2), this option is called differently. On the Remote tab, we select the option "Allow connections from computers running any version of Remote Desktop (less secure)".
We also try disabling Network Level Authentication (NLA) using the Local Group Policy editor – gpedit.msc.
You can either do it by running the gpedit.msc in Windows 10 Home edition or by using the domain group policy management console – GPMC.msc.
In the policy editor we go to the section Computer "Configuration >> Administrative Templates >> Windows Components >> Remote Desktop Services >> Remote Desktop Session Host >> Security", here we find and disable the policy “Require user authentication for remote connections by using Network Level Authentication“.
Additionally, you have to select the "RDP" Security Layer in the "Require use of specific security layer for remote (RDP) connections" policy settings.
Finally, we update the group policies on a local computer (gpupdate / force) or reboot the desktop to apply the new RDP settings.
Method 3
We re-configure the desktops by allowing them to connect to the Remote Desktop with an unsafe version of CredSSP.
In order to do it, we change the registry parameter AllowEncryptionOracle. For that, we run the following command;
REG ADDHKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\CredSSP\Parameters /v AllowEncryptionOracle /t REG_DWORD /d 2Otherwise, you can change the local policy Encryption Oracle Remediation by setting its value to Vulnerable.
This is the only way to access a remote server via RDP if we can’t log in on the server locally (via the ILO, virtual machine console or cloud provider web-interface). Now, connect to a remote server in this mode and install the latest security updates.
After updating the server, we do disable the policy or return the value of the registry parameter AllowEncryptionOracle to 0. Here is the command that to execute;
REG ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\CredSSP\Parameters /v AllowEncryptionOracle /t REG_DWORD /d 0[Are you having troubles with RDP authentication error? – We are available to help you today.]
Conclusion
This article will guide you on methods to fix "RDP authentication error has occurred" which occurs after installing the latest security updates on Windows 10 desktop.
This article will guide you on methods to fix "RDP authentication error has occurred" which occurs after installing the latest security updates on Windows 10 desktop.