Are you trying to set up Zimbra firewall configuration with UFW and firewalld?
This article will guide you through the steps to do this.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to solve Zimbra related queries.
In this context, we shall look into the restoration process of the Zimbra LDAP database from backup.
Steps to install UFW on Ubuntu and CentOS?
Before configuring Zimbra firewall, it is important for you to install UFW and Firewalld.
To install UFW on Ubuntu, simply execute the following command;
sudo apt-get update && sudo apt-get -y install ufwThen for CentOS, the UFW package is available on EPEL repositories. Therefore, execute the following commands;
sudo yum -y install epel-releasesudo yum makecache fastsudo yum -y install ufwHow to Install Firewalld on CentOS 7.x?
If CentOS doesn't have Firewalld already then we can install it by executing the following commands;
sudo makecache fastsudo yum -y install firewalldNext, start and enable the firewalld service by running the command;
sudo systemctl start firewalldsudo systemctl enable firewalldFor Debian based systems, execute the below commands;
sudo apt updatesudo apt -y install firewalldHow to perform Zimbra Firewall configuration using UFW?
Now let us take a quick look at the steps to configure Zimbra firewalld.
For UFW, start by creating an application profile for UFW called Zimbra with the following command;
sudo vim /etc/ufw/applications.d/zimbraNext, add the following contents;
[Zimbra]title=Zimbra Collaboration Serverdescription=Open source server for email, contacts, calendar, and more.ports=22,25,80,110,143,161,389,443,465,514,587,993,995,7071,8443,11211/tcpThen, enable app profile on ufw by executing;
sudo ufw allow Zimbrasudo ufw enableAdditionally, add ssh port by running the following command;
sudo ufw allow sshIn order to make any Zimbra profile then we update it by using the command;
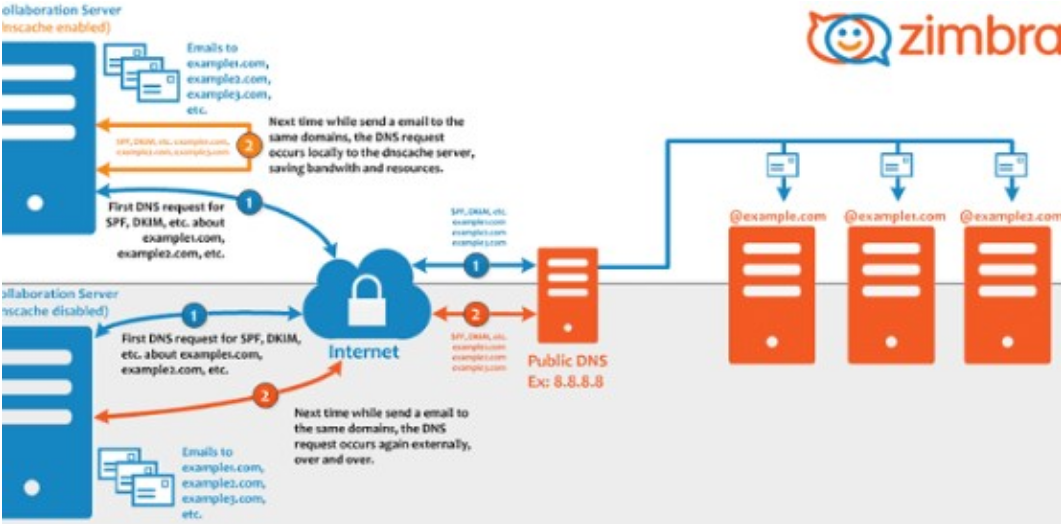
$ sudo ufw app update ZimbraYou will see an output such as;Rules updated for profile 'Zimbra'Skipped reloading firewallFor a single server installation, Memcache is not used outside the local server. We consider binding it to the loopback IP address by running the following commands;
sudo su – zimbrazmprov ms zmhostname zimbraMemcachedBindAddress 127.0.0.1zmprov ms zmhostname zimbraMemcachedClientServerList 127.0.0.1Then, restart the Memcached service;
sudo su – zimbra -c "zmmemcachedctl restart"How to perform Zimbra Firewall configuration using Firewalld?
Start by confirming if firewalld is in a running state or not. To do this, execute;
sudo firewall-cmd –state runningIf not, then we start it by executing the following command;
sudo systemctl start firewalldAfter that, we configure Zimbra ports and services on the firewall. To do this, execute;
sudo firewall-cmd –add-service={http,https,smtp,smtps,imap,imaps,pop3,pop3s} –permanentsudo firewall-cmd –add-port 7071/tcp –permanentsudo firewall-cmd -add-port 8443/tcp –permanentNow, we reload the firewalld configurations by running the following command;
sudo firewall-cmd –reloadThen we confirm the runtime settings by running the following command;
$ sudo firewall-cmd –list-allpublictarget: defaulticmp-block-inversion: nointerfaces:sources:services: dhcpv6-client http https imap imaps pop3 pop3s smtp smtps snmp sshports: 7071/tcp 8443/tcp[Need additional support with Zimbra related queries? – We are here to help you.]
Conclusion
This article will help you to configure Zimbra firewalls with UFW and firewalld.
This article will help you to configure Zimbra firewalls with UFW and firewalld.