Are you trying to know who deleted file/folder from windows server 2016 with audit policy?
Here is a guide on what to do.
Windows Server is a group of operating systems designed by Microsoft that supports enterprise-level management, data storage, applications, and communications.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to fix Windows Server related errors.
In this context, we shall look into how to detect who deleted file / folder in Windows.
How to know Who Deleted File/Folder from Windows Server 2016 with Audit Policy?
Now let’s take a look at how to find who deleted the file/folder from the server.
We make use of the file system object access event auditing to identify a specific user who created, deleted, or modified a specific file.
We shall now see how to configure event auditing for files on a shared network folder on Windows Server 2016. After configuring auditing, we use the information from the Event Viewer to find the user who deleted a specific file on the file server.
However, when we delete a file from a shared network folder, it is deleted immediately instead of being sent to the user’s recycle bin.
How to Enable File and Folder Access Auditing Policy on Windows?
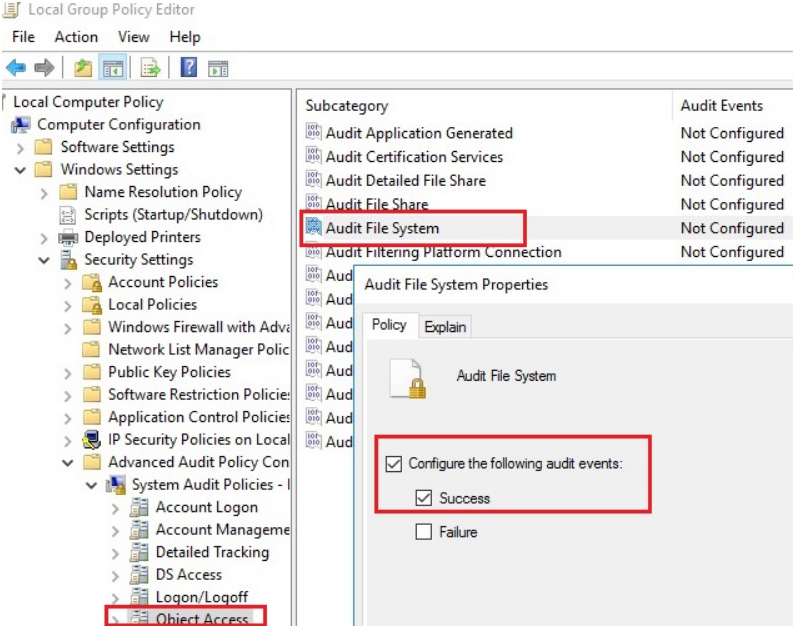
By default, the File System Object Access audit won’t be enabled on Windows Server. We can enable and configure audit settings using Group Policy. Here are the steps that we follow to configure auditing on one server by using the Local Group Policy Editor;
1. First, we open the Local Group Policy Editor console – gpedit.msc.
2. Next, we go to the GPO section with advanced audit policies: Windows Settings >> Security Settings >> Advanced Audit Policy Configuration >> Object Access.
3. After that, we open the Audit File System policy and specify that we want to log only successful access events to file system objects (Configure the following audit events >> Success).
4. Finally, we save the changes and update the local Group Policy settings using the below command;
gpupdate /forceHow to configure File Deleted Audit Settings on a Shared Folder?
Now we configure auditing in the properties of the share network folder to which we want to track access.
1. First, we run File Explorer and open the folder properties. We go to the Security tab and click the Advanced button. Then we go to the Auditing tab.
2. If the message below message appears, click the Continue button.
You must be an administrator or have been given the appropriate privileges to view the audit properties of this object
3. Then we click the Add button to specify the user or group for which we want to capture audit events. If we want to track access events for all users, we do specify the Everyone group.
4. After that, we also specify which permissions used to access the object should be logged. To save only file deletion events in the Event Log, we click the Show advanced permissions button. In the event list, we leave auditing only for the folder and file deletion events – Delete and Delete subfolders and files.
In case, the user deletes any file or folder in the shared network folder. Then the File System -> Audit Success file delete event appears in the Security log with Event ID 4663 from the Microsoft Windows security auditing source.
Then we open the Event Viewer MMC console (eventvwr.msc), expand the Windows Logs -> Security section. Enable event log filter by the EventID 4663.
After that, we open any of the remaining events in the Event Viewer. We see that it contains information about the name of the deleted file, the account of the user who deleted the file, and the process name.
An attempt was made to access an object.
Subject:Security ID: CORP\jon
Account Name: jon
Account Domain: CORP
Logon ID: 0x32B12627
Object:Object Server: Security
Object Type: File
Object Name: E:\Distr\Backup.rar
Handle ID: 0x7bc4
Resource Attributes: S:AI
Process Information:
Process ID: 0x4
Process Name:
Access Request Information:
Accesses: DELETE
Access Mask: 0x10000After enabling file access auditing policy, we can find the below details in the Security log:
i. Who deleted the file from the shared network folder and when it happened
ii. What application (process) was used to delete the file
iii. What is the date of the backup to be restored
How to Write File Deletion Events to SQL Database (MySQL/MSSQL)?
However, even if the audit of the deleted files is enabled, it can be troublesome to find something in the logs. Firstly, it is quite hard to find a specific entry among thousands of events. Secondly, if a file was deleted a long time ago, this event may be absent in the logs, since it was overwritten by new events.
We save all file delete events to the SQL database. For that, we use Microsoft SQL Server, Elasticsearch, or MySQL/MariaDB databases to store the events.
For example, let’s see how to log audit events to a separate database table on MySQL. We can use the following table format:
Server name
Name of the deleted file
Date and time
Name of the user who has deleted the file
The MySQL query to create this table looks like below:
CREATE TABLE deleted_items (id INT NOT NULL AUTO_INCREMENT, server VARCHAR(100), file_name VARCHAR(255), dt_time DATETIME, user_name VARCHAR(100), PRIMARY KEY (ID));To get events with EventID 4663 from the Security log for the current day, we use the following PowerShell script:
$today = get-date -DisplayHint date -UFormat %Y-%m-%d
Get-WinEvent -FilterHashTable @{LogName="Security";starttime=”$today”;id=4663} | Foreach {
$event = [xml]$_.ToXml()
if($event)
{
$Time = Get-Date $_.TimeCreated -UFormat “%Y-%m-%d %H:%M:%S”
$File = $event.Event.EventData.Data[6]."#text"
$User = $event.Event.EventData.Data[1]."#text"
$Computer = $event.Event.System.computer
}
}The next PowerShell script will write the data we get to the MySQL database on a remote server (with the IP address 10.1.1.13):
Add-Type –Path ‘C:\Program Files (x86)\MySQL\MySQL Connector Net 6.9.8\Assemblies\v4.5\MySql.Data.dll’
$Connection = [MySql.Data.MySqlClient.MySqlConnection]@{ConnectionString=’server=10.1.1.13;uid=posh;pwd=P@ssw0rd;database=aduser’}
$Connection.Open()
$sql = New-Object MySql.Data.MySqlClient.MySqlCommand
$sql.Connection = $Connection
$today = get-date -DisplayHint date -UFormat %Y-%m-%d
Get-WinEvent -FilterHashTable @{LogName=”Security”;starttime=”$today”;id=4663} | Foreach {
$event = [xml]$_.ToXml()
if($event)
{
$Time = Get-Date $_.TimeCreated -UFormat “%Y-%m-%d %H:%M:%S”
$File = $event.Event.EventData.Data[6].”#text”
$File = $File.Replace(‘\’,’|’)
$User = $event.Event.EventData.Data[1].”#text”
$Computer = $event.Event.System.computer
$sql.CommandText = “INSERT INTO deleted_items (server,file_name,dt_time,user_name ) VALUES (‘$Computer’,’$File’,’$Time’,’$User’)”
$sql.ExecuteNonQuery()
}
}
$Reader.Close()
$Connection.Close()After saving events to an external database, we can clear this Event log.
Now, to find out who has deleted the file “AnnualReport.DOC“, we run the below script in the PowerShell console;
$DeletedFile = “%AnnualReport.DOC%”
Set-ExecutionPolicy RemoteSigned
Add-Type –Path ‘C:\Program Files (x86)\MySQL\MySQL Connector Net 6.9.8\Assemblies\v4.5\MySql.Data.dll’
$Connection = [MySql.Data.MySqlClient.MySqlConnection]@{ConnectionString=’server=10.1.1.13;uid=posh;pwd=P@ssw0rd;database=aduser’}
$Connection.Open()
$MYSQLCommand = New-Object MySql.Data.MySqlClient.MySqlCommand
$MYSQLDataAdapter = New-Object MySql.Data.MySqlClient.MySqlDataAdapter
$MYSQLDataSet = New-Object System.Data.DataSet
$MYSQLCommand.Connection=$Connection
$MYSQLCommand.CommandText=”SELECT user_name,dt_time from deleted_items where file_name LIKE ‘$DeletedFile'”
$MYSQLDataAdapter.SelectCommand=$MYSQLCommand
$NumberOfDataSets=$MYSQLDataAdapter.Fill($MYSQLDataSet, “data”)
foreach($DataSet in $MYSQLDataSet.tables[0])
{
write-host “User:” $DataSet.user_name “at:” $DataSet.dt_time
}
$Connection.Close()Finally, now, we see the username and the time the file was deleted in the PS console.
How to Log File Delete Audit Events to a Text File?
If we don’t want to use a separate database server, we save file deletion audit events to a plain text log file. For that, we use this PowerShell script to save the output to a text file:
$Outfile = “C:\Logs\Deleted-file-history-log.txt”
$today = get-date -DisplayHint date -UFormat %Y-%m-%d
Get-WinEvent -FilterHashTable @{LogName=”Security”;starttime=”$today”;id=4663} | Foreach {
$event = [xml]$_.ToXml()
if($event)
{
$Time = Get-Date $_.TimeCreated -UFormat “%Y-%m-%d %H:%M:%S”
$File = $event.Event.EventData.Data[6].”#text”
$User = $event.Event.EventData.Data[1].”#text”
$strLog = $Computer + ” ” + $File + ” ” + $Time + ” ” + $User
$strLog | out-file $Outfile –append
}
}[Need urgent assistance in tracking the file/folder deletion queries? – We are here to help you]
Conclusion
This article will guide you on the steps to find out who deleted the file/folder in the Windows server.
This article will guide you on the steps to find out who deleted the file/folder in the Windows server.