Are you facing the error Shorewall forward reject?
This guide is for you.
Shorewall is a firewall tool that makes the task of network security easier. However, the error is the result of rejecting the connection request.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to resolve Shorewall related errors.
In this context, we shall look into how to fix the error, Shorewall forward reject.
What causes Shorewall forward reject error?
We use Shorewall as a firewall for security purposes. The rules added in the Shorewall will reject access from unwanted IP addresses.
All the rules are present in the following configuration file:
/etc/shorewall/rulesRules in this file govern connection establishment. It allows requests and responses automatically using connection tracking.
The rejected/dropped packets logged out of the INPUT or FORWARD chains indicate the following:
1. Users zone definitions screw up and the host sending the packets or the destination host isn’t in any zone.
2. The source and destination hosts are both connected to the same interface and user don't have a policy or rule for the source zone to or from the destination zone or user haven't set the route back option for the interface in /etc/shorewall/interfaces.
3. Two firewall interfaces connect (from different zones) to the same hub or switch.
Now, let us see how to fix this error.
How to fix Shorewall forward reject error?
At Ibmi Media, where we have a great expertise in managing servers, we see many customers face the error, Shorewall forward reject.
Now, let's see how our Support Experts fix it.
Recently, one of the customers approached us with SHOREWALL:FORWARD:REJECT error log from the users /var/log/messages file. The customer was unable to access google.com from his LAN.
While checking Shorewall configuration files, we could trace that the entry ‘all all REJECT info’ in the cat /etc/shorewall/policy Shorewall configuration is the cause of the problem:
cat /etc/shorewall/policy
$FW all ACCEPT
loc $FW ACCEPT
all all REJECT infoThereafter, in order to resolve the issue, we add the following line in the cat /etc/shorewall/policy.
loc net ACCEPT
It indicates that it opens all ports to outside for LAN and so the connection had established.
Similarly, another user came to us with the following error message:
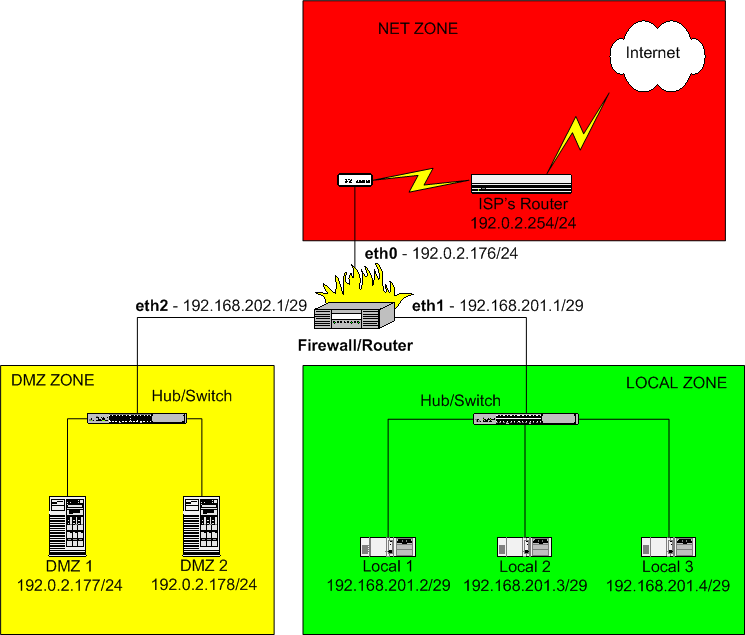
Jun 27 15:37:56 gateway kernel: Shorewall:all2all:REJECT:IN=eth2
OUT=eth1 SRC=192.168.x.x
DST=192.168.x.x LEN=67 TOS=0x00
PREC=0x00 TTL=63 ID=5805 DF
PROTO=UDP SPT=1803 DPT=53 LEN=47On further checking this problem, we traced that 192.168.x.x was in the “dmz” zone and 192.168.x.x is in the “loc” zone. The rule was missing in the configuration file, so we added the following.
Finally, the error had resolved.
[Failed to resolve the Shorewall forward reject error? We'll fix it for you. ]
Conclusion
The 'Shorewall forward reject' error mainly occurs when there is any misconfiguration or missing in the rules added to the Shorewall configuration files.
Shorewall rules file:
Entries in this file govern connection establishment by defining exceptions to the policies laid out in shorewall-policy(5). By default, subsequent requests and responses are automatically allowed using connection tracking.
The 'Shorewall forward reject' error mainly occurs when there is any misconfiguration or missing in the rules added to the Shorewall configuration files.
Shorewall rules file:
Entries in this file govern connection establishment by defining exceptions to the policies laid out in shorewall-policy(5). By default, subsequent requests and responses are automatically allowed using connection tracking.