Are you facing the error ‘libvirtd failed to start’ while manually trying to start libvirt daemon?
This guide will help you.
Sometimes, the libvirt daemon doesn't start automatically. Also, it will fail if we manually start it.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to resolve libvirt related errors.
In this context, we shall look into how to troubleshoot and resolve this error.
How to troubleshoot the error 'libvirtd failed to start' ?
Now let us take a look at how our Support Experts troubleshoot this error message.
1. First, we change libvirt’s logging in /etc/libvirt/libvirtd.conf by enabling the line below. For that, we open the /etc/libvirt/libvirtd.conf file in a text editor.
2. Then we remove the hash (or #) symbol from the beginning of the following line, and save the changes:
log_outputs="3:syslog:libvirtd"We restart libvirt to check if this has resolved the problem.
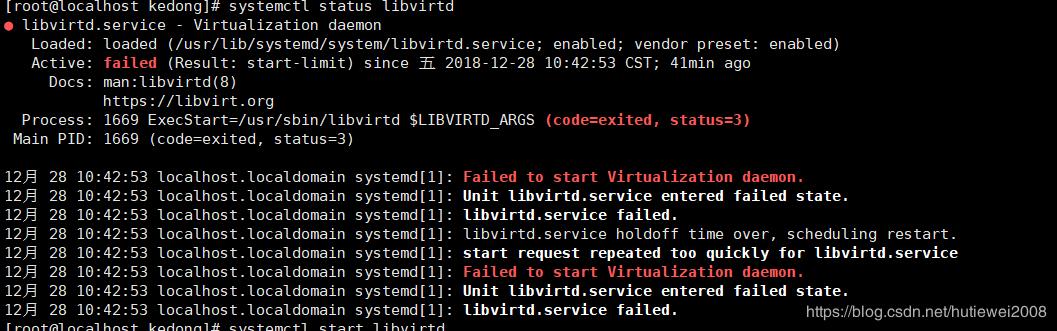
3. If libvirtd still does not start successfully, an error similar to the below will appear:
# systemctl restart libvirtd
Job for libvirtd.service failed because the control process exited with error code. See "systemctl status libvirtd.service" and "journalctl -xe" for details.The libvirtd man page shows that the missing cacert.pem file is used as TLS authority when libvirt is run in Listen for TCP/IP connections mode.
This means the –listen parameter is being passed.
What to do to fix the error 'libvirtd failed to start' ?
You can configure the libvirt daemon’s settings with one of the following methods:
1. Install a CA certificate.
If IdM installation is configured with the integrated Certificate System (CS) certificate authority (CA), we are able to create lightweight sub-CAs. They let us configure services, like virtual private network (VPN) gateways, to accept only certificates issued by one sub-CA. Along with it, we can configure other services to accept only certificates issued by a different sub-CA or the root CA.
To create a new sub-CA named VPN-ca from Web UI:
a. First, we open the Authentication tab and select the Certificates subtab.
b. Next, we select Certificate Authorities and click Add.
c. After that, we enter the name and subject DN for the CA.
The subject DN must be unique in the IdM CA infrastructure.
To create a new sub-CA named vpn-ca from the command line, we run the below command.
[root@server ~]# ipa ca-add vpn-ca –subject=”CN=VPN,O=IDM.EXAMPLE.COM”
——————-
Created CA “vpn-ca”
——————-
Name: vpn-ca
Authority ID: ba83f324-5e50-4114-b109-acca05d6f1dc
Subject DN: CN=VPN,O=IDM.EXAMPLE.COM
Issuer DN: CN=Certificate Authority,O=IDM.EXAMPLE.COMWe run the below command, to verify that the new CA signing certificate has been successfully added to the IdM database:
[root@server ~]# certutil -d /etc/pki/pki-tomcat/alias/ -LTo remove a Sub-CA from the Web UI:
1. First, we open the Authentication tab and select the Certificates subtab.
2. Next, we select Certificate Authorities.
3. After that, we select the sub-CA to remove and click Delete.
4. Finally, we click Delete to confirm.
To delete a sub-CA from the command line, we run the below command:
[root@server ~]# ipa ca-del vpn-ca2. Do not use TLS; use bare TCP instead. In /etc/libvirt/libvirtd.conf set listen_tls = 0 and listen_tcp = 1. The default values are listen_tls = 1 and listen_tcp = 0.
3. Do not pass the –listen parameter. In /etc/sysconfig/libvirtd.conf change the LIBVIRTD_ARGS variable.
[Need urgent assistance with libvirtd related errors? – We are here to help you. ]
Conclusion
This article covers how to resolve the error 'libvirtd failed to start' which happens while manually trying to start libvirt daemon.
To resolve this #libvirtd #error, Try journalctl -u libvirtd.service and see if the full log for the service has more information.
You can manually install "libxslt" to resolve the problem.
Also you can try re-installing the packages that libvirtd/KVM requires and did a full system update.
After that, reboot the server, and libvirtd.service will be working fine.
This article covers how to resolve the error 'libvirtd failed to start' which happens while manually trying to start libvirt daemon.
To resolve this #libvirtd #error, Try journalctl -u libvirtd.service and see if the full log for the service has more information.
You can manually install "libxslt" to resolve the problem.
Also you can try re-installing the packages that libvirtd/KVM requires and did a full system update.
After that, reboot the server, and libvirtd.service will be working fine.