Sometimes when a MySQL client tries to connect to MySQL server over AWS cloud, mysql-server sends back the error, ERROR 2003 (HY000).
Basically, AWS ERROR 2003 (HY000): Can't connect to MySQL server happens When you fail to add the server ip address to the DB security group default policy.
Here at Ibmi Media, as part of our Server Management Services, we regularly help our Customers to perform related AWS queries.
Nature of AWS ERROR 2003 (HY000) Can't connect to MySQL server ?
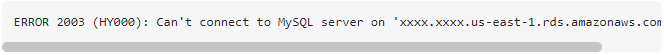
This error may look like the one given below:
RDS : ERROR 2003 (HY000): Can't connect to MySQL server (10060)
The fact is that this error states that the inbound/outbound traffic from the AWS instance is not reachable to the current host where the MySQL client is running. So first a user needs to register the public IP address in the RDS security groups to get access over the RDS MySQL instance.
How to fix AWS ERROR 2003 (HY000) Can't connect to MySQL server ?
Configuring public IP address in security groups will fix "RDS : ERROR 2003 (HY000): Can't connect to MySQL server (10060)".
Apply the following steps to configure public IP addresses in security groups:
1. First, we must find the public IP address for our host machine where we are running mysql-client.
2. Then go to the security groups and add the public IP address for inbound traffic.
3. After that we will add the same entry for outbound traffic distributed by AWS services.
4. Once we complete the above entries we can refresh the security groups and test the connection from any mysql-client.
For example, we can test the connection by simply typing the below command from any terminal where MySQL is configured:
mysql -h host-public-ip/DNS -P 3306 -u username -p password
[Need assistance in fixing MySQL error? We can help you. ]
Conclusion
This article covers methods to tackle AWS "ERROR 2003 (HY000): Can't connect to MySQL server" for our customers.
You can easily fix this issue by adding the public ip address of my EC2 server to the DB security group default policy.
You can create a new security group with the corresponding IP range/subnet of your EC2 instances(s). You can use the exact IP(s), or use your VPC's subnet(s) as the range.
Once created, you can right click your RDS instance in the management console and select 'Modify'. From there, you can change the associated security groups.
This article covers methods to tackle AWS "ERROR 2003 (HY000): Can't connect to MySQL server" for our customers.
You can easily fix this issue by adding the public ip address of my EC2 server to the DB security group default policy.
You can create a new security group with the corresponding IP range/subnet of your EC2 instances(s). You can use the exact IP(s), or use your VPC's subnet(s) as the range.
Once created, you can right click your RDS instance in the management console and select 'Modify'. From there, you can change the associated security groups.